Astrophotography is an awesome passion that’s a mix of science, technology, history, art and dedication. I’m writing this post to share on my journey, not as a way to teach you anything about astronomy, but to offer a window in my life and also show that it’s possible to get started from zero in a new hobby, provided you invest some time into it.
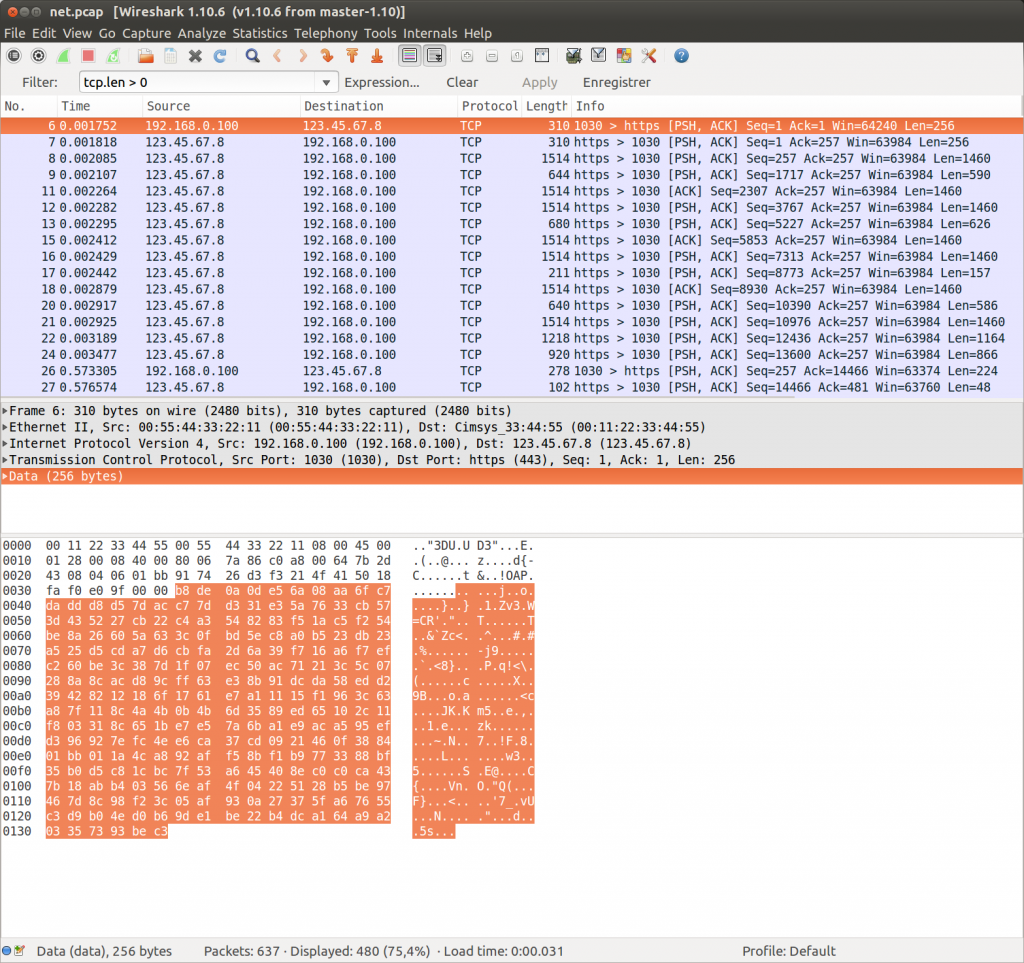
Three years ago, I wrote a blog post on the reasons why I left my job and was pursuing something better suited to my mindset and where healing some wounds wound be possible. I removed it because a person I’d rather not have read it did (if you think it’s you, please return my calls). One or two years before, I started to notice that not only my job had eaten my hobby, but I was less and less interested in computer security and hacking in general – as doing 2 or 3 hours of hacking at home after having spent the day on a pentest was simply not something I enjoyed anymore. It was time for me to be passionate in something else that didn’t involve reading social media for hours (which is unfortunately one of my other hobbies). Maybe go back to something I always loved without taking the time to explore it, partially because I thought that was out of reach or because I should spend all my time trying to be the best hacker in the world (that didn’t work). A few people may know that I was using the handle “spacewalker” until the mid-2000, it didn’t come out of nowhere but from my fascination for the night sky and poor science-fiction cultural references.
Continue reading “My journey to astrophotography (part 1)”


 In July, a
In July, a